Well I didn’t. More specifically I didn’t know that Server 2008 behaves quite differently to 2003 when it comes to choosing a source IP address on a server with multiple IP addresses on the same interface.
Previously on Server 2003 the source address would be the primary address on the interface in question. This address would also register in DNS. Server 2008 and higher uses the address which has the most bits in common with the default gateway. This is worked out in binary and I won’t bore you with the details. To make this a little bit easier on us Microsoft have released a hotfix which introduces the SkipAsSource flag. To use it you have to remove the IP addresses and re-add them using the netsh command.
For example:
netsh Int IPv4 Add Address <Interface Name> <IP Address> SkipAsSource=True
To check that the command worked as expected run:
Netsh int ipv4 show ipaddresses level=verbose
You should see something like this:
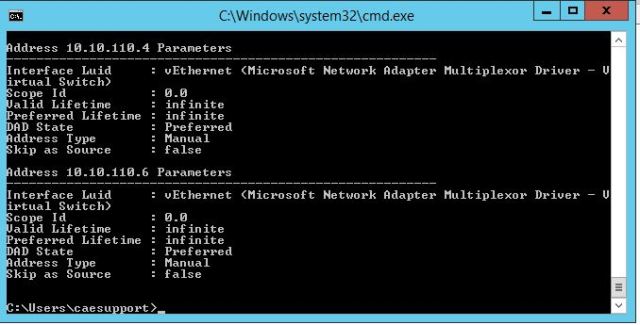
In case you can’t see the Skip as Source setting you still need the install the hotfix above.
You would hope that you’re done at this stage but there are some issues with this hotfix and you will need to install two more:
KB2554859: The “skipassource” flag of IP addresses is cleared after you use the GUI to change IP settings of a network adapter in Windows 7 or in Windows Server 2008 R2
KB2551090: IIS Manager does not display IP addresses that are assigned to the network adapter together with the skipassource flag
This does the trick and gives you control over which addresses are registered in DNS and used as source.
References: